Organizations face mounting pressures to protect sensitive information while also defending against increasingly sophisticated cyber threats. The integration of Certification in Certified Data Privacy Solutions Engineer and the CEH v12 Course (Certified Ethical Hacker version 12) provides a comprehensive framework for professionals looking to enhance their capabilities in data privacy and cybersecurity. By combining these two disciplines, IT experts can ensure that their organizations not only comply with data protection regulations but also safeguard against hacking attempts and data breaches.
Understanding the Importance of Data Privacy and Ethical Hacking

As businesses collect and process vast amounts of personal data, they must prioritize data privacy. CDPSE equips professionals with the skills necessary to implement effective privacy solutions. On the other hand, the CEH v12 Course focuses on teaching advanced hacking techniques, helping professionals understand the mind set of cyber criminals. This dual expertise is critical for organizations aiming to build resilient systems that can withstand attacks while respecting user privacy.
Concepts of Certification: CDPSE
The certification focuses on three core areas:
- Data Governance: Establishing policies and procedures to manage data effectively.
- Data Lifecycle Management: Understanding how data is collected, processed, stored, and disposed of.
- Privacy Architecture: Designing technical solutions that integrate privacy by design into the IT infrastructure.
Concepts of Course: CEH v12

The course equips professionals with advanced hacking techniques, focusing on the latest trends in cybersecurity. Topics include:
- Footprinting and Reconnaissance: Gathering information to identify vulnerabilities.
- Scanning Networks: Utilizing tools that are efficient in scanning to detect open ports and services.
- System Hacking: Exploiting the cause of vulnerabilities to gain unauthorized access.
The Benefits of Combining CDPSE and CEH
By integrating CDPSE knowledge with CEH v12 skills, professionals can approach data privacy and security from multiple angles. This combined expertise enables:
- Proactive Threat Management: Understanding potential hacking techniques allows organizations to fortify their data privacy measures.
- Enhanced Compliance: Knowledge of privacy regulations ensures organizations remain compliant while implementing security protocols.
- Risk Assessment and Mitigation: Professionals can effectively assess risks associated with data handling and hacking attempts.
Skills Comparison
Skill | CDPSE | CEH v12 |
Data Management | Frameworks for governance | Identifying data vulnerabilities |
Risk Assessment | Compliance strategies | Ethical hacking techniques |
Technical Implementation | Privacy architecture | Penetration testing methodologies |
The Integration: Benefits
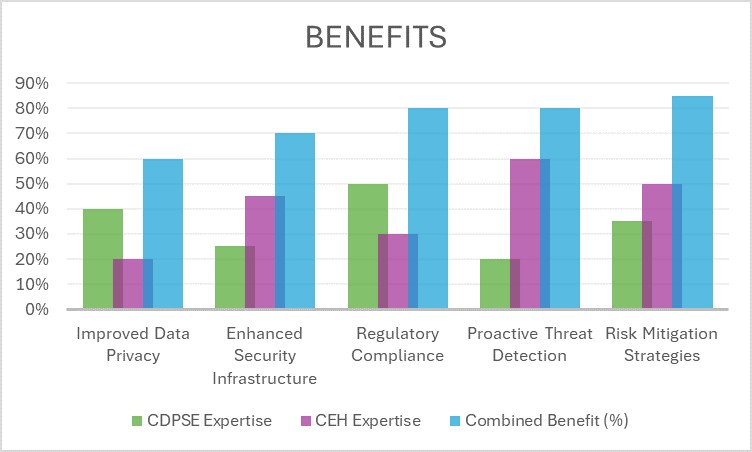
The graph above illustrates how the integration of data privacy expertise from the CDPSE Certification and hacking techniques from the course of Ceh v12 contributes to a more resilient cybersecurity framework. The overlapping benefits highlight the critical need for professionals to understand both fields.
Consider an organization that implemented both CDPSE Certification and CEH v12 training for its IT staff. The results were remarkable:
- Reduction in Data Breaches: The company reported a 40% decrease in data breaches within the first year of training.
- Improved Compliance Rates: Regulatory compliance improved by 30%, leading to fewer fines and legal challenges.
- Enhanced Employee Awareness: Staff awareness of data privacy issues and hacking threats increased significantly, fostering a culture of security.
Conclusion
Combining the knowledge gained from CDPSE and the skills acquired through the CEH v12 certification and courses empowers IT professionals to create a comprehensive approach to data privacy and cybersecurity. In an age where data breaches and privacy violations can severely impact an organization’s reputation, this dual expertise is invaluable. By integrating advanced hacking techniques with robust data privacy frameworks, organizations can not only protect sensitive information but also build trust with their customers. Investing in both areas ensures that IT teams are well-prepared to tackle the challenges of modern cybersecurity, resulting in a more secure and compliant operational environment.



